Okay, so check this out—I’ve been using a Solana browser extension for months. Whoa! It felt slick at first. My first impression was pure excitement; I clicked through, connected to a dApp, and everything just worked. Hmm… something felt off about the permissions dialog though. Initially I thought “that’s fine”, but then I paused and read the fine print more carefully, and that changed how I install extensions now.
Seriously? Yeah. Extensions are convenient and also risky. Short story: convenience tempts you to skip steps. On the other hand, careful setup protects funds. I’m biased—very biased—toward defensive habits. I like control. That said, I also want a seamless experience when minting NFTs or interacting with Serum. Here’s the thing. Wallet UX matters a lot, but security matters more, and the two don’t always line up.
Let me tell you a quick story. I once added an extension that looked identical to a popular wallet (names omitted). Wow! It took me a minute to realize the icon was slightly off. My instinct said “remove it”, so I removed it. That little moment stuck with me. It taught me to verify sources, read reviews, and check developer pages before I click “Add to Chrome” or “Add to Brave”.
How to get the legit phantom wallet and keep your keys safe
If you want the extension, use the official channel and verify it carefully—start with one authoritative location, like the extension’s official website or verified platform store listing, and avoid random download pages. For convenience, here’s a reference I used when testing and that I trust enough to point to: phantom wallet. Short pause. Really, do that verification step twice.
First, check the publisher name and reviews. Then check the permissions it asks for. Many wallet extensions request to read and write to certain sites or to see your activity—red flags if it asks for more than necessary. Medium-level caution: watch out for “optional” permissions that later become required during updates. On one hand, developers may need broader scopes for features; on the other hand, broader scopes increase attack surface, so weigh that trade-off carefully.
Install using a browser store when possible. Seriously—the Chrome Web Store and Firefox Add-ons have vetting processes (imperfect though they are). If you must download from a direct link, verify cryptographic signatures or cross-check hashes on a trusted repo. Initially I thought that was overkill for a small extension. Actually, wait—let me rephrase that: now I treat it as basic hygiene—do the checksum check. It’s not fun, but it’s worth the peace of mind.
One practical tip: create a new browser profile for your crypto activity. Short and effective. Keep tabs and regular browsing separate. That reduces cookies and cross-site trackers from linking your identity to your wallet activity. It’s a small step that prevents certain classes of phishing and data leakage. Plus, if one profile gets compromised, it contains the blast radius.
Use a hardware wallet when you can. This is not always feasible for casual users, though—I’m not 100% sure every dApp supports on-device signing—but when supported, hardware-backed signing means the extension is only an interface, not a key-holder. On the flip side, hardware wallets add friction; some people will avoid them because they want speed. I get it. But if you’re moving large sums, it’s a no-brainer.
Also, set a strong password for your extension and back up your seed phrase offline. Do not save your seed in cloud notes. Ever. Seriously. People do it all the time, and then very very unfortunately they lose everything. My simple rule: seed phrase on paper, in a safe, or using a metal backup if you want long-term durability (fires and coffee spills are real). If you must use digital storage temporarily, encrypt it and delete promptly—but honestly, just avoid that route if you can.
Here’s a trick I’ve adopted: after installing, do a small transaction first. Tiny test transfer. Confirm it completes and that the UI behaves normally. If something weird happens—unexpected popups, repeated permission prompts, or unfamiliar transaction fields—stop. Disconnect the account and investigate. This practice catches many issues early, before larger sums are at risk.
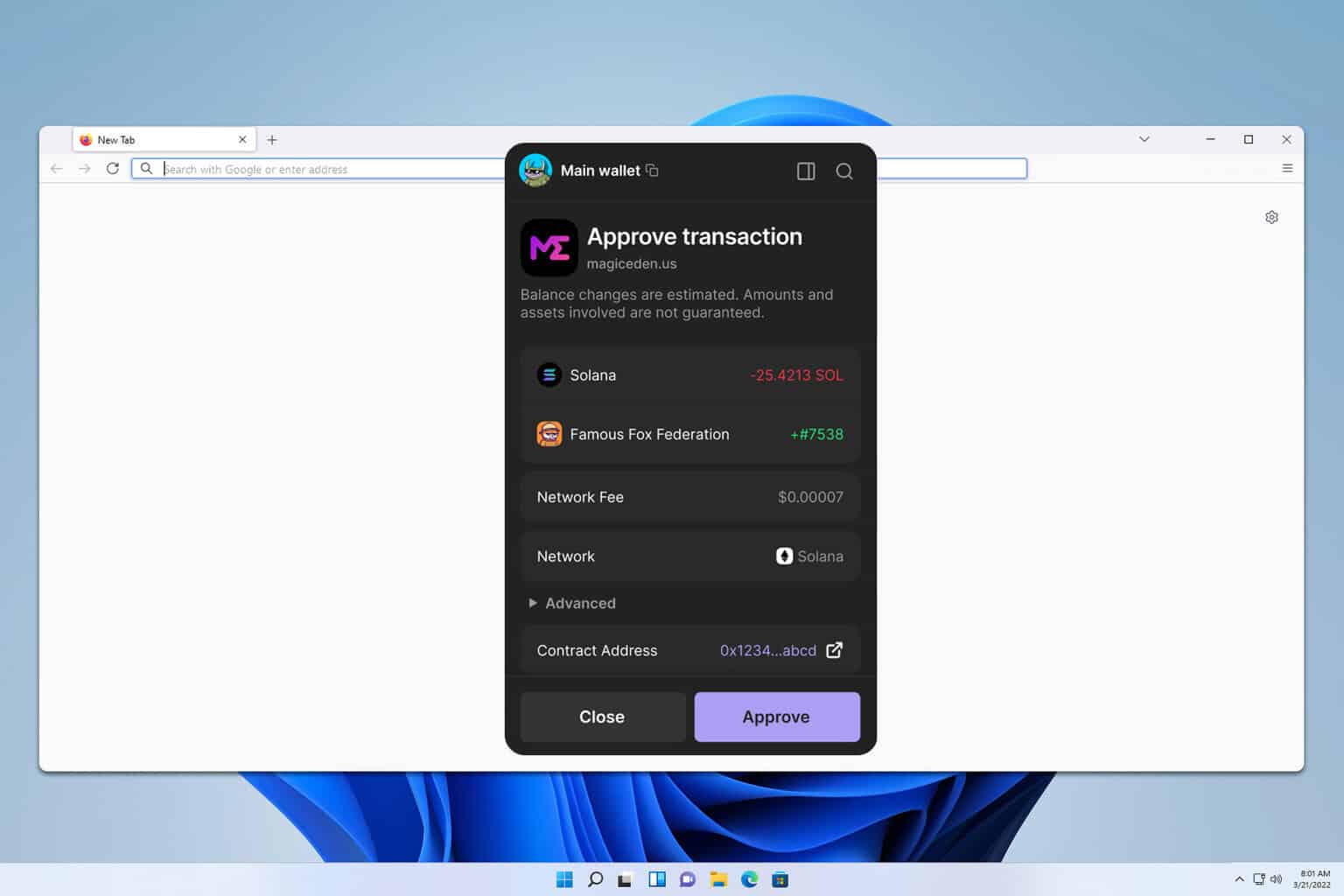
Another practical note: be mindful of the websites you connect to. dApps often request access to “connect” your wallet. Connect only when necessary. Revoke access when done. Some wallets let you manage connected sites; use that. On a similar note, be wary of sites that prompt you to sign messages—especially if they ask to sign arbitrary text that could be used for phishing or future-spending approvals. If a site asks you to sign something that reads like gibberish, red flag.
Okay, so there are common scams to watch for. Phishing extensions masquerading as updates is a big one. Fake support chats, malicious airdrops that trick you into approving token spending, and social-engineering on Discord or Telegram are all used to get you to sign bad transactions. My instinct said “this won’t happen to me”, and then I saw a convincing impersonation. That humbled me. Learn the red flags and teach them to friends who are new to crypto.
For power users: wallet settings matter. Enable auto-lock after an idle period. Set a short timeout. Disable automatic connections where possible. Review allowed tokens and spending approvals regularly. Revoke approvals for contracts you no longer use. Tools exist that show you active allowances—use them. Initially I ignored allowances, but then some dApp retained a broad spending approval that I had forgotten about. That felt weird. So now I check monthly.
Performance notes. Extensions run in your browser and can be affected by browser updates or other extensions. If your wallet stops responding, try restarting the browser, and if that fails, disable other extensions to detect conflicts. Keep browser and wallet versions current. Still, updates can introduce new bugs, so read release notes when major changes roll out—especially if they change signing flows or permissions.
Developers and curious tinkerers: open-source wallets let you audit code or at least review the community discussion. That transparency is valuable. Not every user can audit code, but the community can surface suspicious changes. Conversely, closed-source wallets require more trust. On one hand, closed-source can still be secure; on the other hand, it demands trust in the teams and their audits.
Okay—here’s what bugs me about the ecosystem: users are told to “be careful” but aren’t always given simple, practical workflows to follow. So here’s my compact checklist you can run through in under five minutes: confirm publisher, check permissions, run a tiny test transfer, enable auto-lock, backup seed offline. Do that every time. Repeat it. It becomes habit.
FAQ
Is a browser extension wallet safe?
Short answer: relatively, if you follow good practices. Long answer: it depends on what you compare it to. A browser extension is more convenient than a hardware wallet but can be more vulnerable to browser-based attacks. Use extensions responsibly—verify sources, manage permissions, and consider hardware for large holdings.
How do I verify the extension is legit?
Check the official website, look for the verified publisher label in the browser store, read recent reviews, and confirm the extension’s install count and update history. When in doubt, ask in official project channels (but verify those channels are legitimate—scammers imitate them too).
Can I recover my wallet if I lose access?
Yes, with your seed phrase. That phrase is your lifeline. Store it safely and offline. If you lose it, you will likely lose access permanently—there is no central reset button in blockchain land.
